IACIPP Announces Launch of ‘CIP WEEK’ in Europe


Power/Energy/Oil & Gas sector


The Cybersecurity and Infrastructure Security Agency (CISA) has published a Request for Information from all interested parties on secure by design software practices, including the Shifting the Balance of Cybersecurity Risk: Principles and Approaches for Secure by Design Software whitepaper, as part of its ongoing, collective secure by design campaign across the globe.
To better inform CISA’s Secure by Design campaign, CISA and its partners seek information on a wide range of topics, including the following:
- Incorporating security early into the software development life cycle (SDLC): What changes are needed to allow software manufacturers to build and maintain software that is secure by design, including smaller software manufacturers? How do companies measure the dollar cost of defects in their SDLC?
- Security is often relegated to be an elective in education: What are some examples of higher education incorporating foundational security knowledge into their computer science curricula; When new graduates look for jobs, do companies evaluate security skills, knowledge, and experience during the hiring stage, or are employees reskilled after being hired?
- Recurring vulnerabilities: What are barriers to eliminating recurring classes of vulnerability; how can we lead more companies to identify and invest in eliminating recurring vulnerabilities; how could the common vulnerabilities and exposures (CVE) and common weakness enumeration (CWE) programs help?
- Operational technology (OT): What incentives would likely lead customers to increase their demand for security features; Which OT products or companies have implemented some of the core tenants of secure by design engineering?
- Economics of secure by design: What are the costs to implement secure by design and default principles and tactics, and how do these compare to costs responding to incidents and breaches?
“While we have already received a wide range of feedback on our secure by design campaign, we need to incorporate the broadest possible range of perspectives,” said CISA Director Jen Easterly. Our goal to drive toward a future where technology is safe and secure by design requires action by every technology manufacturer and clear demand by every customer, which in turn requires us to rigorously seek and incorporate input. The President’s National Cybersecurity Strategy calls for a fundamental shift in responsibility for security from the customer to software manufacturers, and input from this RFI will help us define our path ahead, including updates to our joint seal Secure by Design whitepaper.
Co-sealed by 18 U.S. and international agencies, our recent Secure by Design guidance strongly encourages every software manufacturer to build products in a way that reduces the burden of cybersecurity on customers. More recently, CISA launched a new series of Secure by Design Alerts outlining the real-world harms that result from technology products that are not secure by design.
With its partners, CISA encourages technology manufacturers and all interested stakeholders to review the Request for Information and provide written comment on or before 20 February 2024. Instructions for submitting comment are available in the Request for Information. The feedback on current analysis or approaches will help inform future iterations of the whitepaper and our collaborative work with the global community.

Reducing disaster risk is seemingly never-ending in a country like the Philippines, which is exposed to a multitude of natural hazards.
Increasing urbanization also increases the risk of disasters in cities. New patterns of hazards, exposure and vulnerability are emerging. In this context, local authorities play a dual role. They are the first responders to disasters but are also instrumental in disaster risk reduction (DRR).
Persons with disabilities are often the most affected by natural hazards. Little progress has been made over the past decade in including them in DRR, according to a survey conducted by the United Nations Office for Disaster Risk Reduction (UNDRR) in 2023. Persons with disabilities often do not have access to information about disaster risk and are not included in decision-making related to DRR in communities, and few DRR plans consider the specific needs of persons with disabilities. This is the case in the Philippines as in most countries around the world.
A push in the right direction
The Midterm Review of the Sendai Framework for Disaster Risk Reduction 2015-2030, which concluded in 2023, emphasized that more needs to be done to engage the whole of society in DRR, especially the people and communities most at-risk, and that DRR at the local level is of great importance if we want to implement the Sendai Framework by 2030.
Despite the ambitious agenda to localize DRR and the progress that the Philippines has made in increasing capacities and resources and developing regulations at the smallest government units (barangay), its voluntary national report for the Sendai Framework Midterm Review highlights the need to further strengthen local DRR as a priority area.
A chain of learning
On 28 and 29 November 2023, UNDRR provided a training on urban resilience and disability inclusion in DRR in Quezon City, which is the most populous city in the Philippines and belongs to the Metro Manila region. Representatives from different city departments attended, alongside organizations of persons with disabilities.
A key element of the UNDRR-led initiative Making Cities Resilient 2030 (MCR2030) is connecting cities and facilitating peer learning on resilience. A representative from Baguio City in the northern Philippines co-facilitated the training in Quezon City and shared experiences from the inclusion of persons with disabilities in DRR in a context that is familiar to Quezon. In 2022, officials from Baguio City were trained by the MCR2030 Resilience Hub Makati City, which is also part of Metro Manila. Quezon City is thus the third city in this learning chain.
An assessment, an action plan, a platform and lots of commitment
During the training in Quezon City, participants learned how to use the Disaster Resilience Scorecard for Cities and its annex for the inclusion of persons with disabilities in DRR to evaluate disaster risk management practices.
Based on this assessment, they developed an initial action plan on the inclusion of persons with disabilities in institutional capacities, infrastructure resilience, and recovery, including “Building Back Better”.
The aim of the training was not only to increase knowledge about inclusive DRR and risk assessment capacities, but also to build a platform where local authorities and persons with disabilities come together to discuss DRR and where persons with disabilities are involved in risk assessments and decision-making on DRR.
For many representatives from organizations of persons with disabilities, this training was the first time they had been included in discussions about DRR. “We appreciate the opportunity to have a seat at the table and contribute to decisions that concern us”, one representative said.
Together, the city officials and the organizations of persons with disabilities committed to making DRR in Quezon City more inclusive and to transfer their knowledge and lessons learnt to other cities.
Support for local DRR from the national authorities
With the Department of the Interior and Local Governments (DILG) and the Office for Civil Defense (OCD), national authorities were also represented at the workshop.
An official from the OCD highlighted that the inclusion of persons with disabilities is an issue that needs to be further considered in policies and frameworks, at the local and national levels. “The training helped to understand that local planning needs to be more inclusive and also take into account the needs and perspectives of persons with disabilities to build resilience”, he said.
The engagement of national authorities in MCR2030 builds capacity for urban resilience also at the national level, helping to ensure that cities are more resilient to future disasters and the most at-risk are protected.
[Source: Making Cities Resilient 2030 (MCR2030) United Nations Office for Disaster Risk Reduction - Regional Office for Asia and Pacific]
Critical Infrastructure Protection & Resilience North America, taking place on 12th-14th March 2024 in Lake Charles, Louisiana, and co-hosted by IACIPP and Infragard Louisiana, has announced the Preliminary Conference Program for the 2024 conference and exhibition, and you can download the agenda at www.ciprna-expo.com/PSG.
The Guide provides you the outline program, excellent international expert speakers and schedule of events to help you plan your participation.
You can also register online today and save with the Early Bird delegate rates at www.ciprna-expo.com/register
Confirmed Speakers include:
– Dr David Mussington, Executive Assistant Director for Infrastructure Security, Department of Homeland Security (DHS), Cybersecurity and Infrastructure Security Agency (CISA)
- Brian Harrell, VP & Chief Security Officer, AVANGRID
- Michael Hill, Program Specialist, Cybersecurity and Infrastructure Security Agency
- Emilio Salabarria, Senior Program Manager for Cybersecurity, The Florida Center for Cybersecurity: Cyber Florida
- Dr. Srinivas Bhattiprolu, Global Head of Advanced Consulting Services, Nokia
- Ed Landgraf, Chairman, Coastal And Marine Operators
- Kimberly Heyne, ChemLock Program Manager, Cybersecurity and Infrastructure Security Agency (CISA)
- Dan Frazen, CO-CEM, Agriculture Emergency Coordinator (All-Hazards), Colorado Department of Agriculture
- Dr. Joshua Bergerson, Principal Infrastructure Analyst, Argonne National Laboratory
- Chris Essid, Sector Branch Chief, Cybersecurity and Infrastructure Security Agency (CISA)
- Budge Currier, Assistant Director Public Safety Communications, California Office of Emergency Services (Cal OES)
- Terrence Check, Senior Legal Council, CISA
- Rola Hariri, Defense Industrial Base Liaison, Cybersecurity and Infrastructure Security Agency (CISA)
- Lester Millet, President, Infragard Louisiana & Safety Risk Agency Manager, Port of South Louisiana
- Michael Finch, Technology Services Director, Lane County Department of Technology Services
- Richard Tenney, Senior Advisor, Cyber, Cybersecurity and Infrastructure Security Agency (CISA)
- Andrew A Bochman, Senior Grid Strategist-Defender, DOE / Idaho National Lab
- Jim Henderson, CEO, Insider Threat Defense Group
Full speaker list: www.ciprna-expo.com/speakers2024
Download Agenda: www.ciprna-expo.com/PSG
Schedule of Events/Agenda: www.ciprna-expo.com/schedule
List of Exhibitors: www.ciprna-expo.com/exhibition/exhibitors
Registration: www.ciprna-expo.com/register
Join the community in Lake Charles on 12th-14th March 2024 for some more great discussions on securing America's critical infrastructure and assets.
As someone responsible in your organisations for critical assets and/or infrastructure, Critical Infrastructure Protection and Resilience Europe is the leading conference that will keep you abreast of the changes in legislation, current threats and latest developments.
Download the Preliminary Conference Programme Guide at www.cipre-expo.com/guide.
What is the new directive on the Resilience of Critical Entities...
The Directive on the Resilience of Critical Entities entered into force on 16 January 2023. Member States have until 17 October 2024 to adopt national legislation to transpose the Directive.
The Directive aims to strengthen the resilience of critical entities against a range of threats, including natural hazards, terrorist attacks, insider threats, or sabotage, as well as public health emergencies.
Are you up to date on this legislation, and do you know what you need to do to be compliant?
Get updated on the NIS2 Directive and what it means to you...
An important discussion will centre around the EU cybersecurity rules introduced in 2016 and updated by the NIS2 Directive that came into force in 2023. It modernised the existing legal framework to keep up with increased digitisation and an evolving cybersecurity threat landscape.
By expanding the scope of the cybersecurity rules to new sectors and entities, it further improves the resilience and incident response capacities of public and private entities, competent authorities and the EU as a whole.
Businesses identified by the Member States as operators of essential services in the above sectors will have to take appropriate security measures and notify relevant national authorities of serious incidents. Key digital service providers, such as search engines, cloud computing services and online marketplaces, will have to comply with the security and notification requirements under the Directive.
What will this mean for you and how can you meet the Directives goals?
Critical Infrastructure Protection and Resilience Europe is Europe's leading discussion that brings together leading stakeholders from industry, operators, agencies and governments to collaborate on securing Europe's critical infrastructures.
The conferences top quality programme looks at these developing themes and help create better understanding of the issues and the threats, to help facilitate the work to develop frameworks, good risk management, strategic planning and implementation.
The packed event themes include:
- Interdependencies and Cascading Effects
- Emerging Threats against CI
- Crisis Management, Coordination & Communication
- Power & Energy Sector Symposium
- Government, Defence & Space Sector Symposium
- Communications Sector Symposium
- Information Technology (CIIP) Sector Symposium
- Transport Sector Symposium
- CBRNE Sector Symposium
- Technologies to Detect and Protect
- Risk Mitigation and Management
- The Insider Threat
- Business Continuity Management
- EU Horizon Projects Overviews
You are invited to be a part of this program, where you can meet, network and learn from the experiences of over 40 expert international speakers, as well as industry colleagues who share the same challenges and goals.
Please join us and the CI industry in the beautiful city of Prague, on 3rd-5th October, for a great programme of discussions that can help you to deliver enhanced security and resilience for your organisation.
Visit www.cipre-expo.com for further details

Please find here your downloadable copy of the Summer 2023 issue of Critical Infrastructure Protection & Resilience News for the latest views and news at www.cip-association.org/CIPRNews.
- The CNI / Crowded Places Security Debate
- Beyond Physical Protection
- Hybrid Threats
– A Comprehensive Resilience Ecosystem
- Artificial Intelligence and Cybersecurity Research
- Resilience in action
- An Interview with EU-CIP Project
- IBM Report: Half of Breached Organizations Unwilling to Increase Security Spend Despite Soaring Breach Costs
- Using the EU Space Programme for disaster risk management in Hungary
- An Interview with TIEMS
- Critical Infrastructure Protection and Resilience Europe Preview
- Agency and Industry News
Download your Critical Infrastructure Protection & Resilience News at www.cip-association.org/CIPRNews
Critical Infrastructure Protection and Resilience News is the official magazine of the International Association of Critical Infrastructure Protection Professionals (IACIPP), a non-profit organisation that provides a platform for sharing good practices, innovation and insights from Industry leaders and operators alongside academia and government and law enforcement agencies.
#CriticalInfrastructureProtection #CriticalInfrastructure #cybersecurity #help2protect #cisa #ciprna #cipre #resilience #cooperation #emergencymanagement #emergencyresponse #crisismanagement #businesscontinuity #crisisresponse #mitigation

The theft of nuclear material and the compromise of information could have devastating consequences. Threats can come from external adversaries or from "insiders," including employees or visitors with trusted access. In 2014, DOE established its Insider Threat Program to integrate its policies, procedures, and resources. The program also coordinates analysis, response, and mitigation actions among DOE organizations.
The House report accompanying a bill for the National Defense Authorization Act for fiscal year 2022 includes a provision for GAO to review DOE's efforts to address insider threats with respect to the nuclear security enterprise. This report examines (1) the extent to which DOE has implemented required standards to protect the nuclear security enterprise from insider threats and (2) the factors that have affected DOE's ability to fully implement its Insider Threat Program.
GAO reviewed the minimum standards and best practices for federal insider threat programs, DOE documentation, and four assessments by independent reviewers. GAO also interviewed DOE and National Nuclear Security Administration officials and contractors.
The Department of Energy has several programs to ensure proper access to and handling of the nation's nuclear weapons and related information. DOE started a program in 2014 to further protect against insider threats from employees, contractors, and trusted visitors.
But as of 2023, DOE hasn't fully implemented the program. For example, DOE doesn't ensure that employees are trained to identify and report potential insider threats. Also, the agency hasn't clearly defined contractors' responsibilities for this program.
DOE changed the program's leadership in February 2023, but there's more to do. We recommended ways to improve the program.
The Department of Energy (DOE) has not implemented all required measures for its Insider Threat Program more than 8 years after DOE established it in 2014, according to multiple independent assessments. Specifically, DOE has not implemented seven required measures for its Insider Threat Program, even after independent reviewers made nearly 50 findings and recommendations to help DOE fully implement its program (see fig. for examples). DOE does not formally track or report on its actions to implement them. Without tracking and reporting on its actions to address independent reviewers' findings and recommendations, DOE cannot ensure that it has fully addressed identified program deficiencies.
Examples of Selected Recommendations from Independent Assessments of DOE's Insider Threat Program
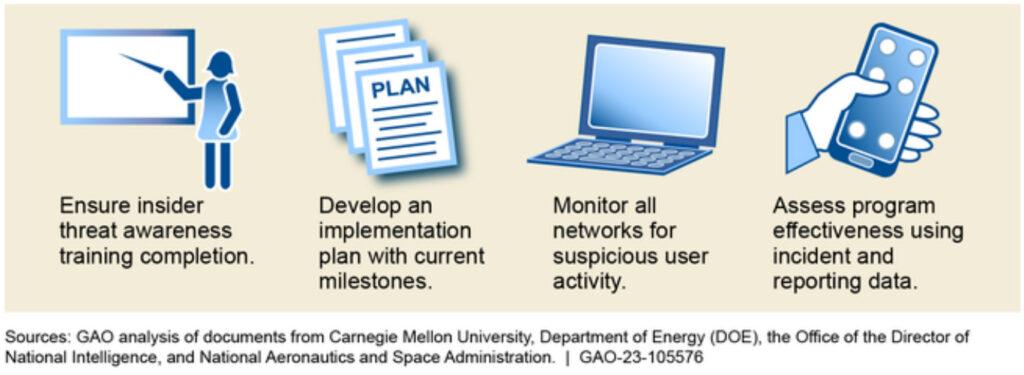
DOE has not fully implemented its Insider Threat Program due to multiple factors.
- DOE has not integrated program responsibilities. DOE has not effectively integrated Insider Threat Program responsibilities. Instead, DOE divided significant responsibilities for its program between two offices. Specifically, the program's senior official resides within the security office, while operational control for insider threat incident analysis and response resides within the Office of Counterintelligence—a part of the organization with its own line of reporting to the Secretary of Energy. Without better integrating insider threat responsibilities between these offices, DOE's insider threat program will continue to face significant challenges that preclude it from having an effective or fully operational program.
- DOE has not identified and assessed resource needs. DOE has not identified and assessed the human, financial, and technical resources needed to fully implement its Insider Threat Program. Program funding identified in DOE's budget does not account for all program responsibilities. For example, DOE's budget does not include dedicated funding for its contractor-run nuclear weapons production and research sites to carry out their responsibilities for implementing the program. Unless DOE identifies and assesses the resources needed to support the Insider Threat Program, it will be unable to fully ensure that components are equipped to respond to insider threat concerns, potentially creating vulnerabilities in the program.
The Commission directed NERC to evaluate whether the physical security protection requirements in NERC’s Reliability Standards are adequate to address the risks associated with physical attacks on BPS Facilities. Specifically, FERC directed NERC to conduct a study evaluating the following: (1) the adequacy of the Applicability criteria set forth in the Physical Security Reliability Standard; (2) the adequacy of the required risk assessment set forth in the Physical Security Reliability Standard; and (3) whether a minimum level of physical security protections should be required for all BPS substations and their associated primary control centers.
The purpose of the CIP-014 Reliability Standard is to “identify and protect Transmission stations and Transmission substations, and their associated primary control centers, that if rendered inoperable or damaged as a result of a physical attack could result in instability, uncontrolled separation, or Cascading within an Interconnection.”2 The standard requires applicable Transmission Owners (“TOs”) to perform periodic risk assessments of their applicable transmission stations and transmission substations (hereinafter collectively referred to as “substations”) to identify which of their applicable substations are “critical” to BPS reliability (which, for purposes of CIP-014, is whether instability, uncontrolled separation, or Cascading would result if the substation were damaged or rendered inoperable). The TO must then perform an evaluation of the potential physical security threats and vulnerabilities of a physical attack to each of their “critical” substations and develop and implement a documented physical security plan to address those threats and vulnerabilities. Additionally, for each primary control center that operationally controls an identified substation, the applicable Transmission Operator (“TOP”) must perform an evaluation of the potential physical security threats and vulnerabilities of a physical attack to that control center and develop and implement a documented physical security plan to address those threats and vulnerabilities.
As discussed within this report, NERC finds that the objective of CIP-014 appropriately focuses limited industry resources on risks to the reliable operation of the BPS associated with physical security incidents at the most critical facilities. Based on studies using available data, NERC finds that the CIP-014 Applicability criteria is meeting that objective and is broad enough to capture the subset of applicable facilities that TOs should identify as “critical” pursuant to the risks assessment mandated by Requirement R1. NERC did not find evidence that an expansion of the Applicability criteria would identify additional substations that would qualify as “critical” substations under the CIP- 014 Requirement R1 risk assessment. Accordingly, at this time, NERC is not recommending expansion of the CIP-014 Applicability criteria.
NERC acknowledges, however, that supplementary data3 could show that additional substation configurations would warrant assessment under CIP-014. Accordingly, NERC plans to continue evaluating the adequacy of the Applicability criteria in meeting the objective of CIP-014. Following issuance of this report, NERC will work with FERC staff to hold a technical conference to, among other things, identify the type of substation configurations that should be studied to determine whether any additional substations should be included in the Applicability criteria. The technical conference would also help establish data needs for conducting those studies
NERC finds, however, that the language in Requirement R1 of CIP-014 should be refined to ensure that entities conduct effective risk assessments of their applicable substations. Information from ERO Enterprise Compliance Monitoring and Enforcement Program (“CMEP”) activities indicates that while the overall objective of the CIP-014 Requirement R1 risk assessment is sound, there are inconsistent approaches to performing the risk assessment. The ERO Enterprise observed that, in certain instances, registered entities failed to provide sufficient technical studies or justification for study decisions resulting in noncompliance. NERC finds that the inconsistent approach to performing the risk assessment is largely due to a lack of specificity in the requirement language as to the nature and parameters of the risk assessment. Accordingly, NERC will initiate a Reliability Standards development project to evaluate changes to CIP-014 to provide additional clarity on the risk assessment.
As discussed further below, the objective of the Reliability Standards development project would be to:
• Clarify the risk assessment methods for studying instability, uncontrolled separation, and Cascading; such as the expectations of dynamic studies to evaluate for instability.
• Clarify the case(s) used for the assessment to be tailored to the Requirement R1 in-service window and correct any discrepancies between the study period, frequency of study, and the base case a TO uses.
• Clarify the documentation, posting, and usage of known criteria to identify instability, uncontrolled separation, or Cascading as part of the risk assessment. The criteria should also include defining “inoperable” or “damaged” substations such that the intent of the risk assessment is clear.
• Clarify the risk assessment to account for adjacent substations of differing ownership, and substations within line-of-sight to each other.
Finally, while NERC is not recommending an expansion of the CIP-014 Applicability criteria at this time, NERC finds that, given the increase in physical security attacks on BPS substations, there is a need to evaluate additional reliability, resiliency, and security measures designed to mitigate the risks associated with those physical security attacks. As discussed further below, establishing a uniform, bright line set of minimum physical security protections for all (or even an additional subset of) BPS substations and associated primary controls centers, is unlikely to be an effective approach to mitigating physical security risks and their potential impacts on the reliable operation of the BPS. While a uniform set of minimum level of protections could potentially prevent some forms of physical security threats, NERC finds that such a pursuit lacks the application of a risk-based approach to expending industry resources, fails to provide for a methodical approach necessary to address site-specific threats or objectives (as expected using a design basis threat process), and does not consider the need for other reliability, resiliency, and security measures to mitigate the impact of a physical attack. These combined measures provide increased operational and planning capability as well as improved effectiveness of local network restoration. NERC finds that this more holistic approach will provide greater long-term flexibility and minimize the impacts of physical attacks on BPS reliability.
Full report can be found here >>
Protecting critical infrastructure that helps provide necessities like water, electricity, and food is a national priority. Events like natural disasters or cyberattacks can disrupt services Americans need for daily life.
We testified that many federal agencies work to protect the nation's critical infrastructure and look to the Cybersecurity and Infrastructure Security Agency for leadership on how to do it.
A 2021 law expanded these agencies' responsibilities and added some new ones. CISA is working on guidance and more to help agencies implement these responsibilities. We've recommended that CISA set timelines for completing this work.
The William M. (Mac) Thornberry National Defense Authorization Act for Fiscal Year 2021 expanded and added responsibilities for Sector Risk Management Agencies (SRMAs). These agencies engage with their public and private sector partners to promote security and resilience within their designated critical infrastructure sectors. Some officials from these agencies described to GAO new activities to address the responsibilities set forth in the act, and many reported having already conducted related activities. For example, the act added risk assessment and emergency preparedness as responsibilities not previously included in a key directive for SRMAs. New activities officials described to address these responsibilities included developing a communications risk register and developing emergency preparedness exercises.
The Department of Homeland Security's (DHS) Cybersecurity and Infrastructure Security Agency (CISA) has identified and undertaken efforts to help SRMAs implement their statutory responsibilities. For example, CISA officials stated they are updating key guidance documents, including the 2013 National Infrastructure Protection Plan and templates for revising sector-specific guidance documents. CISA officials also described efforts underway to improve coordination with sector partners, such as reconvening a leadership council. SRMA officials for a majority of critical infrastructure sectors reported that additional guidance and improved coordination from CISA would help them implement their statutory responsibilities. However, CISA has not developed milestones and timelines to complete its efforts. Establishing milestones and timelines would help ensure CISA does so in a timely manner.
Why GAO Did This Study
Critical infrastructure provides essential functions––such as supplying water, generating energy, and producing food––that underpin American society. Disruption or destruction of the nation's critical infrastructure could have debilitating effects. CISA is the national coordinator for infrastructure protection.
The William M. (Mac) Thornberry National Defense Authorization Act for Fiscal Year 2021 includes a provision for GAO to report on the effectiveness of SRMAs in carrying out responsibilities set forth in the act. This statement addresses (1) how the act changed agencies' responsibilities, and the actions agencies have reported taking to address them; and (2) the extent to which CISA identified and undertook efforts to help agencies implement their responsibilities set forth in the act.
This statement is based on GAO's February 2023 report on SRMA efforts to carry out critical infrastructure protection responsibilities and CISA's efforts to help SRMAs implement those responsibilities. For that report, GAO analyzed the act and relevant policy directives, collected written responses from all 16 sectors using a standardized information collection tool, reviewed other DHS documents, and interviewed CISA officials.
In its February 2023 report, GAO recommended that CISA establish milestones and timelines to complete its efforts to help sector risk management agencies carry out their responsibilities. DHS concurred with the recommendation. Additionally, GAO has made over 80 recommendations which, when fully implemented, could help agencies address their statutory responsibilities.

Senior officials from NATO and the European Union met to launch a new NATO-EU Task Force on Resilience of Critical Infrastructure. Cooperation to strengthen critical infrastructure has become even more important in light of the sabotage against the Nord Stream pipelines, and Russia’s weaponisation of energy as part of its war of aggression against Ukraine.
First announced by NATO Secretary General Jens Stoltenberg and European Commission President Ursula von der Leyen in January, the initiative brings together officials from both organisations to share best practices, share situational awareness, and develop principles to improve resilience. The Task Force will begin by focusing on four sectors: energy, transport, digital infrastructure, and space.
Announcing the initiative in January, Mr Stoltenberg said: "We want to look together at how to make our critical infrastructure, technology and supply chains more resilient to potential threats, and to take action to mitigate potential vulnerabilities. This will be an important step in making our societies stronger and safer."
NATO-EU cooperation has reached unprecedented levels in recent years, and particularly since the start of Russia’s war of aggression against Ukraine. In January, NATO and EU leaders signed a new joint declaration to take partnership between the organisations to a new level, including on emerging and disruptive technologies, space, and the security impact of climate change.